AttackIQ is an American software company that was recently hit with a brand impersonation attack, also known as brandjacking, that was traced back to a group of cybercriminals operating out of Iran.
The hackers registered a top-level domain that was similar to AttackIQ (domain squatting) and then attempted to create a fake website that was intended to be part of a phishing campaign designed to trick customers into clicking on a phony link, which would lead them to a fake page where they would unwittingly divulge personal data.
According to a detailed analysis of the attack published by AttackIQ, “The original malware was identified through open-source intelligence and sandboxing telemetry. Researchers monitoring these resources noticed malware using a derivative of the AttackIQ name. At the same time, the threat intelligence community observed a new top-level domain register ‘attackiq.ir’, subsequently publishing the fake website and mimicking the AttackIQ website.”
Without open-source intelligence (OSINT), the attack probably would have succeeded. The phishing emails would have lured unsuspecting customers to the fake site, those customers would probably have had their credit card numbers or their identities stolen. And the blame would have fallen on AttackIQ and those responsible for their security.
Incidents like these can potentially cause serious and long-lasting brand damage to organizations, resulting in lost revenue over the course of many years. According to the Ponemon Institute, the average cost of a data breach in the U.S. is $4.24 million, with 38% of that cost attributed to lost customers and the cost of acquiring new customers.
However, thanks to OSINT, AttackIQ was able to get ahead of the attack and have the fake website taken down before any brand damage was done.
Types of Brand Impersonations
Hijacking a corporate brand can involve domain spoofing, social media impersonation, and fake emails designed to launch ransomware or other types of attacks. There are many types of brand impersonations.
1. At its most harmless, the hacker takes over a social media account and posts silly or obviously fake information. For example, a hacker recently took over the Twitter account for the H.J. Heinz Co. and posted items such as: “Why not try Heinz beans on toast.”
2. A more troubling example would be when an attacker took over the account of Twitter CEO Jack Dorsey in 2019 and posted racial slurs.
3. Another type of brand impersonation is the sale of counterfeit goods bearing the company’s brand or logo. According to a recent report, trade-in fake or stolen goods accounts for 3.3% of global trade and is steadily increasing.
4. And there’s the AttackIQ example, the phishing/spoofed website type attack in which unsuspecting customers could have had their personal data stolen.
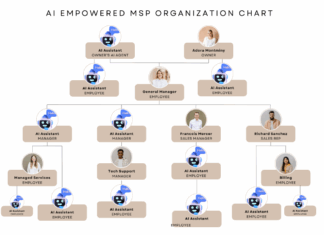
What MSPs Can Do
The best way to minimize the impact of brand impersonations is to prevent them from happening in the first place. By using a platform that consolidates intelligence from multiple OSINT tools, MSPs can detect potential brandjacking incidents across all of their clients before they occur.
If an incident does take place, OSINT tools can help MSPs quickly identify and block the attack before the damage is done – potentially saving millions of dollars in lost customer trust and lost business.
OSINT techniques can also detect and investigate the appearance of counterfeit goods sold online, along with country-specific steps to report fraudulent activity. OSINT can spot mentions of your brand, search social media platforms and secondary marketplace to look for unauthorized sales promotions.
The only way to spot these threats is to have visibility across the Surface, Deep and Dark Web and to be able to consolidate intelligence into actionable information. Media Sonar equips security teams with the ability to conduct digital investigations to stay one step ahead of the attackers.
Resources
Media Sonar is constantly performing research to keep up with the latest trends and best practices for security professionals. Here are a few resources that you or your colleagues might find useful.
- Download the on-demand webinar Defending Digital Risk Profiles
- Get access to the report OSINT for Brand Protection
- Read the article Mandatory Ransomware Reporting & The Opportunity for MSPs